Update: The cards are not being replaced. See a statement by the Transport Ticketing Authority at the bottom of the article.
blog Victoria’s troubled Myki public transport smartcard project has suffered another high profile setback, with the state reported to be replacing over a million of the cards following revelations they can be hacked for free transport. The Melbourne Times Weekly reports:
“German engineering academics David Oswald and Christof Paar, both from Ruhr Universitat Bochum, have been studying how to hack into the card and claim their research forced [Myki manufacturer] NXP to discontinue the Myki card. The scientists are studying the cards as part of their cryptography research.”
The move is the latest in a series of problems for the Myki project. Alleged improprieties in contractual processes, delays and glitches — Myki has had every issue in the book. But at least Victorians can stand proud and acknowledge Myki largely was implemented and does work — unlike New South Wales’ botched Tcard equivalent.
update: Transport Ticketing Authority chief executive Bernie Carolan has posted the following statement on the Myki website, clarifying that the organisation will not be replacing any Myki cards already owned by customers:
The Transport Ticketing Authority (TTA) has no intention of replacing any myki cards already owned by customers, as erroneously reported by some media outlets. The TTA believes that myki customers do not need to worry about the security of their myki card.
It is important to note that no personal information is stored on a myki card. Only the card balance and past 10 transactions are held on the card. Mifare DESFire is the safest smart card available on the market. It is far more technologically advanced than other models.
There are four separate security measures that can be installed to minimise the chances of this sort of attack and myki cards have all four. These relate to security key diversification, fraud detection countermeasures, blocking of fraudulent cards and an additional binding of card information.
Advice in a statement issued by the chip’s manufacturer indicates that laboratory conditions, very expert knowledge and plenty of time is required to carry out the claimed attack. It cannot be done simply by walking past a cardholder.
The TTA believes that myki customers do not need to worry about the security of their myki card. The only information available to a hacker would be the card balance and last 10 transactions. If one of the 10 previous transactions was a top up, no banking details are recorded on the myki card, just the amount added.
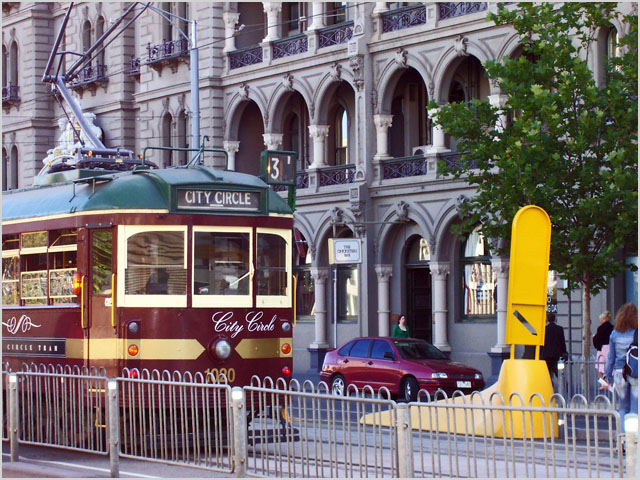
Image credit: Benjamin Diehl, royalty free

Bzzt, Renai. You fell for popularist tech reporting. Seriously, a MSM article with “hacker” in the title? Did a tram need to fall from the sky for you to get your skepticism pants on?
Everything you needed to understand that was even in the article. The old MIFARE Classic cards aren’t being made anymore because although they are cheap they are insecure. However, Myki/Kamco knew this and there are security countermeasures that ban that card’s unique ID once any tampering is detected. The newest most secure cards (the “MIFARE DESFire EV1”) require different programming initially, the TTC is working out how to manage that migration/upgrade.
Look, it even says clearly: “TTA chief executive Bernie Carolan said the hacks didn’t force the authority to replace the cards.” The cards aren’t being replaced, only new cards will be on new stock.
Might want to look at the MyKi website, they’re not going to replace the cards because “no personal information is stored on a myki card”. I personally use MyKi on a daily basis as my main method for getting to uni. I’m not worried too much, but I’m a little concerned about it.
Either way, the statement from the TTA can be found here: http://www.myki.com.au/
I will repeat what I have said on another forum. It is unlikely any cards will be replaced until their four year expiry dates, which would place the first to be replaced (from regional Victoria) from December next year.
Oyster in London has been ‘vulnerable’ to a security flaw in the previous ‘Mifare Classic’ model for some years now – but for various reasons mass cloning of cards in that system is not viable. They are slowly moving to the DESFire EV1 which myki will now do as well.
—
The DESFire attack is a ‘side-channel attack’ which looks for electromagnetic radiation emitting from the circuitry inside the chip itself (to see what 1’s and 0’s are flying around). It is much harder than the attack on Mifare Classic which found a flaw in the cards software.
Having poked a myki with an NFC reader, I can say a few things about the security of it:
1. No data on the myki or the short term ticket is readable without authenticating with a known key first.
2. The secret key is never passed over the air (unlike Mifare Classic) – rather a three way handshake is used
3. The encryption itself is 3DES (AES in EV1)- and if an attack was found on that, all the banks in the world will be running for cover.
4. Further security can be achieved by encrypting over-the-air transmissions as well; I don’t know if myki readers do this.
5. Also, there can be different keys for reading, writing, creating and deleting data.
Personally I think an easier attack would be to get ones hands on a myki machine (CVM or bus console), give yourself lots of topups/encode many short term tickets and then remove all evidence (transaction log, money) anything took place.
Cheers for the feedback on this, everyone. I hear you loud and clear — will fix the article tomorrow morning (Friday).
When NFC chips are standard in smartphones it will be interesting to see how much more readily systems like this are vulnerable to skimming/cloning
Much easier to upgrade the software in a phone, than a non internet connected card though.
Security updates will be easier to propagate.
Interesting, but I was thinking more about the potential for using NFC-equipped phones to skim/clone the cards…
get with the program everybody if it has a chip,strip or brain of any kind it will be hacked welcome to the future of our world sad isn’t it people with nothing better to do than stuff peoples lives up should have their fingers smacked with a big hammer what sort of morons will our children have to deal with in forty years time with the technology they will have
Comments are closed.