
news The Federal Government has categorically bungled the implementation of its controversial Data Retention policy, with data released by the Communications Alliance today showing the Attorney-General’s Department has proven comprehensively unable to successfully administer the scheme.
The Government’s Data Retention legislation passed Parliament in March this year. It requires that all Australian telecommunications carriers store significantly more data on their customers than they were previously holding, including records pertaining to all emails, telephone calls and SMS messages. The scheme was slated to come into effect today.
However, today the peak industry representation group, the Communications Alliance, released data showing that the Attorney-General’s Department has proven unable to administer the scheme successfully.
The survey — which polled many dozens of Australian telecommunications companies — showed that the majority had lodged so-called implementation plans with the Attorney-General’s Department detailing their plans to implement the scheme.
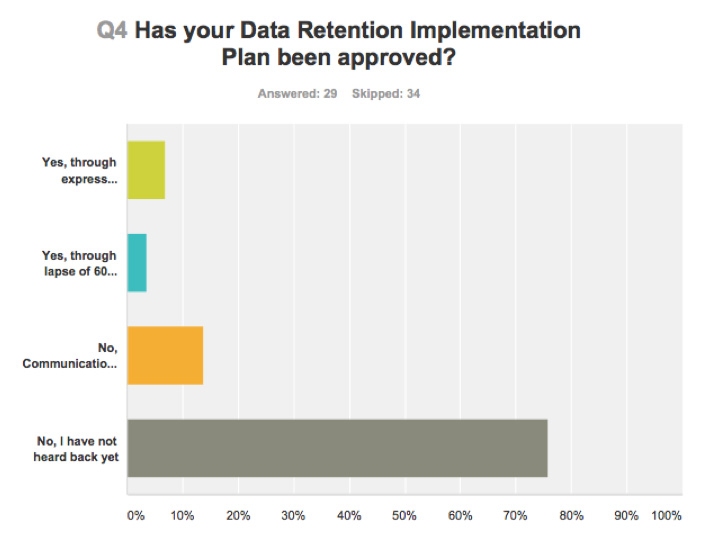
However, the data also showed that the Government had not proven able to approve the vast majority of implementation plans, with most telcos never having heard back from the Attorney-General’s Department, despite complying with the law and filing their implementation plan. Attorney-General George Brandis oversees the department.
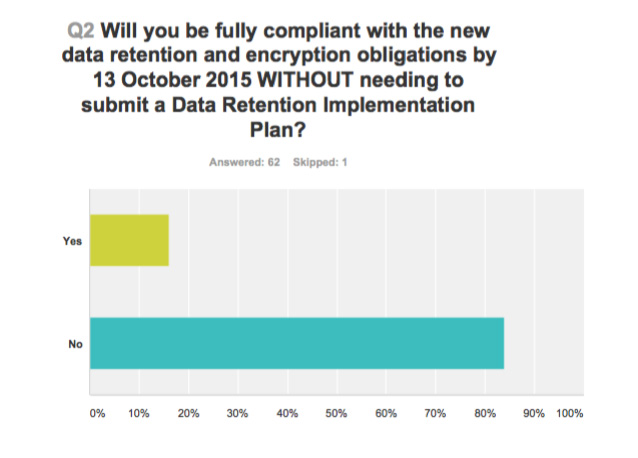
As a result, about 82 percent of the 63 companies who responded to the survey will not be compliant with the legislation which comes into force today, despite their own best efforts.
The survey found that over two thirds of companies who responded were not confident at all or only somewhat confident that they had actually understood what exactly is required of them under the scheme. Only 16 percent are ‘ready’ to retain and encrypt the data as required.
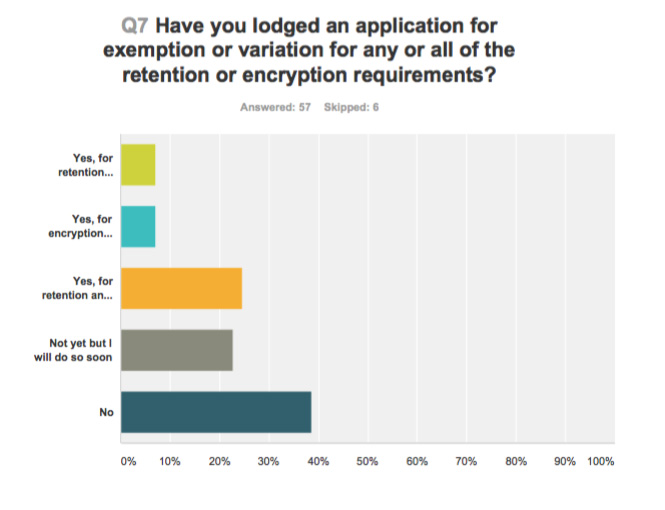
Further, most ISPs have lodged, or plan to lodge, applications for exemptions from particular aspects of the Data Retention scheme which they find difficult to comply with.
Communications Alliance chief executive John Stanton said the results highlighted the magnitude of the challenge ahead for all stakeholders if the industry was to achieve compliance with the new laws.
“It is no surprise that many service providers won’t be compliant when the legislation comes into force — many of these because they are still waiting to hear from Government as to whether their implementation plans have been approved,” he said.
Before the legislation was passed in March, most of the major players in Australia’s telecommunications industry (Telstra, Optus, iiNet and so on) filed a joint letter with the Government, seeking certainty regarding how much of their implementation costs they could expect to be reimbursed by the Government. However, Stanton noted that the ISPs had still — more than six months later, and with the scheme supposed to go live today — to receive any certainty on the issue.
The survey indicates that costs for implementing the scheme cover an extremely wide range — from less than $1,000 to more than $10 million.
“All providers are still waiting to hear from Government as to how it will apportion the $131.3 million that has been pledged in assistance to partially meet the set-up costs that service providers – and ultimately their customers – are facing as a result of the regime.”
“The Government has indicated it will consult with industry in coming weeks on how to apportion the subsidy and this remains an urgent task, as service providers are now having to commit to investment decisions without knowing how much of that spending will remain unfunded.”
“In light of the survey results, the onus remains on Government to work constructively with industry – and not rush to enforcement – over coming months to help providers come into line with what is proving to be a very challenging and somewhat confusing impost on the industry.”
The full survey results can be downloaded in PDF format here.
Image credit: CeBIT, Creative Commons

VPN technology could be used to remain unaffected from such data retention law. A normal internet user or business could connect to any VPN company based out of USA, Australia or Europe like “PureVPN” to remain secure.
why would they want to retain VPN metadata? The vast majority of it is point of sale data between stores and their head offices.
meta data for vpn can still be useful in correlation attacks. people have been caught who used TOR this way.. not as useful, but still useful.
Recently, Rightscorp, the leading anti-piracy firm, managed to win a patent to safeguard against piracy, in the wake of Australia becoming the worst country for piracy concerns. he Data Retention Australia law is here!
What’s a VPN and how does it work?
A VPN encrypts traffic between two end points on the Internet creating a secure tunnel that does not let any external entity to intervene; note that it has nothing to do with providing access to internet. The regular Internet traffic goes directly from you to the websites (and other resources) you connect to, and back. Your ISP transmits all your Internet packets for you.
What is your ISP capable of?
Everything you do is visible to the ISP. The ISP knows where you are connecting to and can read all your unencrypted traffic. The ISP charges you for the access to internet, which is a must-have if you need to browse online and therefore carries a high price. An ISP can even hack into your computer if he wants to and there’s nothing you can do about it.
How would a VPN save you?
A VPN can be referred to as an extension that provides secure browsing over the internet. As described earlier, a secure tunnel won’t let your ISP or even the government spy on you or your activities. And if the ISP grows suspicious, then there’s feature call Split tunneling available in limited VPNs such as Ivacy VPN (https://www.ivacy.com/ ). This feature lets you decide what you want to show to your ISP, and what you don’t. The activities that you don’t want to share with your ISP will stay hidden.
Good for nothing fascists and their fascist fraud schemes to defend their fascism and their corporate donors.
Don’t ever give Liberals control of anything to do with technology, they are techno illiterate idiots and like to distract and avoid answering questions for as long as possible.
Crudely expressed but imo very accurate!
Welcome to Corporate sponsored Fascism folks, see the TPP if in doubt (oh wait, you cant it’s secret … wonder why!!!)
Hahaha yeah and Labor are so much better… lets face it, with the exception of maybe a few ministers the vast majority on all sides of politics haven’t got a f***ing clue when it comes to technological decisions
Absolute fucking circus. It’s mind boggling that more than half the country wants to vote these people back in.
This is not a Lib vs Lab issue. They are both guilty in this. Let’s not forget that they both voted for this.
Both parties failed by voting for this but it is up to the current government to implement and administer it.
On both counts they failed.
and this is why we should have been voting Green.
Who had the most sensible policy when it came to the NBN, the economy, the environment (duh), who would be protecting the privacy of australians whilst disengaging from conflicts that make us a target in the eyes of extremists.
I’m sure some shrill is going to reply with some sort of quote from a Murdoch rag supposedly showing a ‘loony green’ or better still some banal and vexatious insult about how the Greens are crazy.
You know what? Id actually like to see the Greens get a shot at a term running the country… It would be interesting to watch another party fuck it all up for a change
Lab voted for it sure, but it’s Lib who have completely failed in implementing it. It’s one thing to create a fascist policy, quite another to turn ISPs into criminals and force them to close for financial reasons by failing to fulfill your share of the responsibility.
I guess I should pay more attention, you basically said that *facepalm*
#LibLabLast #rebootau
This survey covers the top tier ISPs. If they are struggling, imagine what’s going on with the hundreds of smaller operators who are not members of the Communications Alliance.
I’m convinced this is about internal politics. When Brandis has to admit policy failure both he and it will go.
I’m the mean time the PM can just stand back and wait.
The compliance burden on ISPs is something that is too often overlooked here. The cost to have staff review each request to validate it’s source (is this from an approved agency/our approved contact within that agency), scope (is the metadata requested within that agency’s remit), and legal standing (is a warrant required, and has it been correctly completed) is going to exceed by orders of magnitude any technical costs of retention/recovery. Given that similar interactions, and requests can take hours to resolve, and verify how can we hope to see even the most profitable ISPs come through this intact? Especially given that ACMA has previously reported more than half a million requests per annum, and this number can only be expected to rise as the quantity, and scope of retained data increases, and more agencies gain access.
The problem is they can’t validate it. Eg if it’s data of a jerno like Renai the telcos have to accept the word of the law enforcement asking the request has followed the right procedures it even worst that the judge providing over the request doesn’t get to know why they want to access the data
The former data access legislation did not need a judge to approve its access. Are you sure this does?
My understanding is that certain agencies have warrantless access, where if it is similar to the current system, they can simply complete a form and lodge it with providers to request the data. Warrants are only required by agencies who do not have access to this data by default.
“Warrants are only required by agencies who do not have access to this data by default.”
Section 282 and 283 states that service providers are obliged to provide law enforcement with anything they’ve aske for as long as its in relation to a crime.
The form that they send (which i had a hand in creating many many years ago) doesn’t provide any sort of information that would allow a provider to verify that a crime has occurred. Basically if they receive it from the agencies communication centre then they are obliged to provide the requested data.
The only except and only time a warrant is required is in relation to a intercept.
However with all this data they don’t need to listen to a coded conversation. With surveillance data (photos, number plates etc) combined with the years of medata they can get now law enforcement agencies will be able to prove probable cause without any problem. They’ll get their warrants from a judiciary that is utterly beholden to the police and feds.
I’d imagine one of the first steps the law enforcement agencies will do with this data is use it to discover the relationships their own officers have with certain individuals. They’ll subsume the data into their own data warehouses and crunch it. Creating pretty maps of relationships.
One if you if you reverse searched peodphiles going back several years what relationships you’ll find?
I don’t get why the ALP was so quick to back the Liberals on this. The entire act went through parliament with amazing efficiency, almost unheard of in Canberra.
What’s going on? What is the real story? Who are the real targets?
And that’s where it’s up the ISP/Telco. They can just accept every single request at face value, or they can take the time to confirm, and check all the information to ensure that each request is compliant.
I know which I would prefer them to do.
I know which one they do any time a customer lodges a FOI request.
But we also know that for most, the almighty dollar will guide them far more than ethics, and the protection of their customers.
Judge is only needed for jernos and the ISP will still have know idea if the law enforcement has gone to a judge or not
ISP is breaking law if they divulge a journalists metadata without a warrant. But how does ISP determine that a warrant less request does not relate to a journo? They can’t without asking the person involved.
The ISP don’t know what data they need to keep and based on an interview on ABC radio this morning the AG still doesn’t know either despite it ‘being clearly defined in the legislation’ (paraphrasing the AG when he avoided answering the question).
TIL: The fact that laws that are designed to not be fully implemented until mid-2017 are not implemented today is evidence that they’ve been “comprehensively bungled”. The majority of the industry seems to be using the implementation plan process contained in the laws to, you know, implement this over the full two year window.
I know you don’t like data retention Renai. But this site has always been about impartial reporting and not hyperbole.
ISPs will comply, because they have to.
It’s very apparent that the Government has rushed the solution, without the department actually being in a place to action any of it in a timely manner; let alone the ISPs who pretty much have to describe their process.
Which is pretty common for any number of rushed solutions. The press will still report the situation as a bit of a cluster-fuck – because really it actually is. The timelines were beyond hopeful and into the realms of fancy.
Minister: We need to retain the metadata’s they might escape to who knows where!
Industry: Why?
Minister: Jehadis!!!!1
Industry: No really, why?
Minister: I have reasons but for operational matters I can’t tell you what they are.
Industry: Wait, how are we supposed to pay for this?
Minister: Submit a plan on how you’ll retain the metadata lest it escapes!
Industry: But how are we supposed to pay for this?
Minister: OPERATIONAL MATTERS. METAS ESCAPING. STOP THE DATA!
Industry: …
Industry: fine, here is a proposal on how we can store (massively invasive) data about people
Minister: BROFIST!
Industry: .. it’s 500 pages, took ages to prepare and cost quite a bit
Minister: STOP THE META CAN’T YOU SEE IT’S ESCAPING
Industry: it will take us months to put the equipment in that you want
Minister: BUT THE METAS. THEY ARE TRYING TO QUEUE JUMP.
Industry: you are instituting a massive surveillance state that might make us unprofitable
Minister: METAS. EEK WHAT MIGHT THEY DO IN THE WILD?
Industry: minister we need more time
Minister: NO TIME. ONLY JEHADI METAS ESCAPING! STOP THE METAS.
Industry: you don’t actually know what you want, do you.
Minister: CAN’T TALK; FIGHTING METAS
Industry: but how are we supposed to pay for this?
Minister: OPERATIONAL MATTERS. METAS ESCAPING. STOP THE DATA!
Best comment ever :)
I am sure you missed these comment “Turn back the DATAS, Any DATAS that arrive by boat will turned back around”
and
“DATAS arriving by sea funds terrorists”
the weak fear the weaker and attempt to take liberty from the strong to fight a war that they create to appease their insecurity when it was their insecurity which made them weak. what a pack of bloody galahs.
So do Government Depts that supply internet to their staff classify as an ISP? Do they have to retain data, and are they ready to comply ?
The reason for this mess is obvious, just look at George Brandis eyes in the picture at the top, George has been smoking too much pot.
I emailed an ISP on this during the week, asking a direct question on whether or not metadata was being (or would be) stored when we use their SMTP server.
I received a copy of their _privacy policy_ back in response.
I’ve since asked them to clarify with a Yes or a No.
This is going to get rather messy methinks.
Can we get someone (eg Senator Ludlam) to propose a law that would require the post office to keep a 2-year record of every letter they send? After all, metadata is just like the information on the outside of a letter, right?
Or even better, can we get said senator to propose a law that would require people in Australia to have a GPS tracker implanted at birth (or at the airport for tourists)? Why use half-measures of tracking everyone’s location through their phone, when some terrorists might not even have phones!!
It’s really a cool and helpful piece of information. I am satisfied that you just shared this helpful info with us.
Please keep us informed like this. Thanks for sharing.
Comments are closed.